In today’s interconnected world, safeguarding patient data is paramount. This exploration delves into the crucial intersection of health information systems and data privacy, focusing on the comparative effectiveness of two prominent approaches: DHIS2, a widely used platform for health data management, and FAIR data principles, which promote data accessibility and reuse.
We’ll unpack the core functionalities of DHIS2, its built-in security features, and its limitations concerning data privacy. Simultaneously, we’ll examine the four FAIR data principles – Findable, Accessible, Interoperable, and Reusable – and their implications for health data management. The goal is to understand how these approaches can be leveraged to create robust, secure, and privacy-conscious health information systems.
Introduction
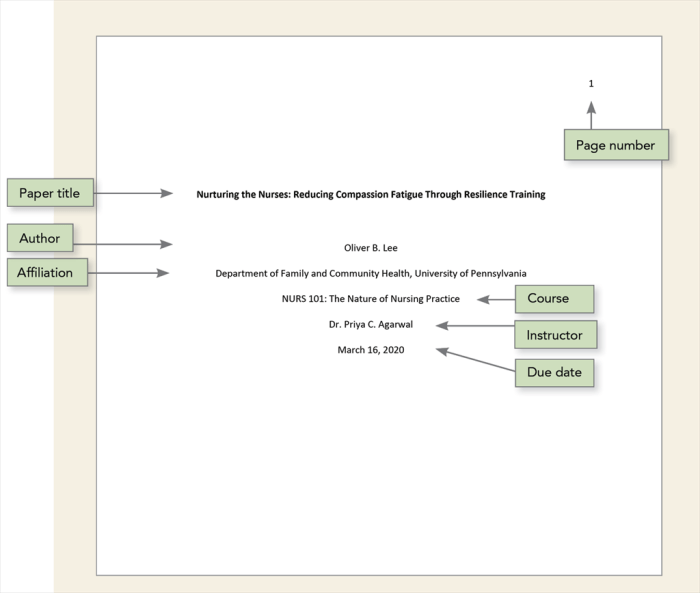
Source: apa.org
Data privacy is paramount in today’s world, especially when dealing with sensitive information like health data. The rise of global health initiatives and the increasing reliance on digital health systems have amplified the need for robust data protection measures. Safeguarding patient information is not just an ethical imperative but also a crucial factor in maintaining public trust and ensuring the effectiveness of healthcare programs.
This discussion explores the comparative effectiveness of two approaches – DHIS2 and FAIR data principles – in addressing these crucial data privacy challenges.
Significance of Data Privacy in Global Health
Data privacy is fundamental to the success of global health initiatives. These initiatives often involve the collection, storage, and sharing of vast amounts of health-related data, including personal medical histories, treatment plans, and demographic information. The confidentiality of this data is essential for several reasons:
- Patient Trust and Participation: Patients are more likely to participate in health programs and share accurate information when they trust that their data will be kept private. Breaches of privacy can erode this trust, leading to reduced participation and less reliable data.
- Ethical Considerations: Respecting patient privacy is a core ethical principle in healthcare. It aligns with the principles of autonomy, beneficence, and non-maleficence, ensuring that individuals have control over their health information.
- Legal and Regulatory Compliance: Data privacy is increasingly regulated by laws and standards such as GDPR, HIPAA, and other country-specific regulations. Non-compliance can result in significant financial penalties and reputational damage.
- Preventing Discrimination and Stigma: Protecting health data helps prevent discrimination and stigma. For example, information about a patient’s HIV status or mental health condition could be used to discriminate against them if not properly protected.
- Promoting Data Quality and Accuracy: When patients trust that their data is protected, they are more likely to provide accurate and complete information, leading to better data quality and more effective healthcare interventions.
DHIS2 Platform and Health Data Management
DHIS2 (District Health Information Software 2) is a widely used, open-source platform for collecting, managing, analyzing, and visualizing health data. It is deployed in numerous countries around the world, particularly in resource-constrained settings, to support health information systems (HIS). The platform offers a range of functionalities that include:
- Data Collection: DHIS2 allows for the collection of data from various sources, including health facilities, community health workers, and surveys.
- Data Storage: The platform provides a secure database for storing health data, with options for data encryption and access control.
- Data Analysis: DHIS2 includes tools for analyzing data, generating reports, and creating visualizations, such as maps and charts.
- Data Sharing: The platform supports data sharing with other systems and organizations, enabling interoperability and collaboration.
- User Management and Security: DHIS2 provides robust user management features, allowing administrators to define roles and permissions to control access to sensitive data. This helps in implementing privacy controls and ensuring that only authorized personnel can view or modify specific information.
DHIS2’s modular design and flexibility make it adaptable to diverse health contexts. It’s often used to track disease outbreaks, monitor health service delivery, and evaluate the impact of health interventions. However, the platform’s ability to protect data privacy is crucial, especially as it handles increasingly sensitive information.
FAIR Data Principles and Data Accessibility
FAIR data principles aim to make data Findable, Accessible, Interoperable, and Reusable. These principles are designed to improve data management and facilitate data sharing, while also considering privacy concerns. They provide a framework for creating data that is more valuable and useful for research, policy-making, and other purposes. The core principles are:
- Findable: Data should be easy to find, with rich metadata that describes its content, origin, and characteristics. This includes assigning unique and persistent identifiers (like DOIs) and registering data in searchable repositories.
- Accessible: Data should be accessible, ideally through open and standardized protocols. This may involve providing clear access conditions and authentication mechanisms, while also considering privacy restrictions.
- Interoperable: Data should be able to be combined with other data sets, which requires using standardized formats, vocabularies, and ontologies.
- Reusable: Data should be clearly licensed and described, so that it can be used for different purposes. This includes providing sufficient information about the data’s provenance, quality, and limitations.
The FAIR principles are not inherently privacy-focused, but they can be applied in a way that respects data privacy. For example, data can be made FAIR while also being anonymized or de-identified to protect patient confidentiality. This approach balances the need for data accessibility with the need for privacy protection.
The Growing Need for Robust Data Privacy Solutions
The demand for robust data privacy solutions is increasing due to several factors. These include:
- Increasing Data Volume: The volume of health data is growing exponentially, driven by the adoption of electronic health records, wearable devices, and other technologies. This vast amount of data creates new challenges for data privacy.
- Cybersecurity Threats: Healthcare organizations are increasingly targeted by cyberattacks, which can result in data breaches and the exposure of sensitive patient information.
- Data Sharing Requirements: There is a growing need to share health data for research, public health surveillance, and other purposes. However, data sharing must be done in a way that protects patient privacy.
- Evolving Regulations: Data privacy regulations are constantly evolving, with new laws and standards being introduced around the world. Healthcare organizations must stay up-to-date with these regulations to avoid legal and financial penalties.
- Public Awareness: Public awareness of data privacy issues is growing, and patients are increasingly concerned about how their health data is used. This requires healthcare organizations to be transparent about their data privacy practices.
The convergence of these factors underscores the critical need for effective data privacy solutions. The comparative analysis will explore how DHIS2 and FAIR data principles can be used to meet these challenges, ensuring that health data is both accessible and protected.
Understanding DHIS2
DHIS2, or District Health Information Software 2, is a widely used open-source platform for collecting, validating, analyzing, and visualizing health data. It is a key tool in many countries for managing health information systems (HIS). Understanding its core functionalities, privacy features, and limitations is crucial for assessing its effectiveness in a comparative study alongside FAIR data approaches.
Core Functionalities of DHIS2
DHIS2 offers a comprehensive suite of functionalities that support the entire data lifecycle, from collection to reporting. These features are designed to facilitate efficient health data management.
- Data Collection: DHIS2 supports various data collection methods, including web forms, mobile applications, and offline data entry. This flexibility allows for data capture from diverse sources, even in resource-constrained settings. Users can define data elements, indicators, and data entry forms tailored to their specific needs.
- Data Storage: Data is stored in a structured database, typically PostgreSQL. This structured approach ensures data integrity and facilitates efficient querying and analysis. The system supports version control, allowing for tracking of data changes over time.
- Reporting and Analysis: DHIS2 provides powerful reporting and analytical capabilities. Users can generate a wide range of reports, including tables, charts, and maps. The platform supports the creation of custom dashboards and data visualizations to monitor key health indicators. Data can be exported in various formats for further analysis.
Built-in Privacy Features and Security Measures within DHIS2
DHIS2 incorporates several built-in features to protect data privacy and security, designed to adhere to data protection best practices.
- Access Control: Role-based access control (RBAC) is a core security feature. Users are assigned roles with specific permissions, limiting their access to data based on their responsibilities. This prevents unauthorized access to sensitive information. For example, a data entry clerk might only have access to enter data, while a system administrator has full control.
- Encryption: DHIS2 supports encryption of data at rest and in transit. This ensures that data is protected from unauthorized access, even if the storage or communication channels are compromised.
- Audit Trails: The system maintains detailed audit logs, recording all user activities, including data access, modifications, and deletions. This allows for tracking of data changes and identification of potential security breaches. The audit trails are crucial for accountability and data integrity.
- Data Validation: Built-in data validation rules help to ensure data quality and integrity. This reduces the risk of errors and inconsistencies in the data, which can compromise data privacy.
Limitations of DHIS2 Regarding Data Privacy
Despite its security features, DHIS2 has limitations that can impact data privacy. Understanding these limitations is important for a complete assessment.
- Data Granularity: The level of detail at which data is stored can be a privacy concern. Highly granular data, such as individual patient records, can be more vulnerable to re-identification.
- User Error: Human error, such as incorrect data entry or misconfiguration of security settings, can lead to privacy breaches. Training and awareness are crucial to mitigate this risk.
- System Configuration: The security of DHIS2 depends heavily on its configuration. Improperly configured systems can be vulnerable to attacks.
- Third-Party Integrations: Integrations with other systems can introduce vulnerabilities. Data shared with or received from external systems needs to be carefully managed.
DHIS2 Handling of Data Anonymization and De-identification Techniques
DHIS2 offers some support for data anonymization and de-identification, but the extent and effectiveness of these techniques depend on how they are implemented.
- Data Masking: DHIS2 allows for data masking, where specific data elements are hidden or replaced with generic values. For example, patient names can be replaced with unique identifiers.
- Aggregation: Aggregating data at higher levels (e.g., district level instead of individual clinics) can reduce the risk of re-identification.
- Pseudonymization: While not a core feature, DHIS2 can be configured to use pseudonymization techniques, where identifying information is replaced with pseudonyms.
- Limited Built-in Functionality: It’s important to note that DHIS2 does not offer advanced anonymization features by default. Implementation of robust anonymization techniques often requires external tools or custom development.
DHIS2’s Security Features
This table summarizes key security features in DHIS2.
| Security Feature | Description | Implementation | Impact on Privacy |
|---|---|---|---|
| Access Control | Role-based access control to limit data access. | Users are assigned roles with specific permissions. | Reduces the risk of unauthorized data access. |
| Encryption | Encryption of data at rest and in transit. | Implemented through configuration of the DHIS2 instance and database. | Protects data from unauthorized access, even if storage or communication channels are compromised. |
| Audit Trails | Detailed logs of user activities. | Enabled by default, records data access, modifications, and deletions. | Allows for tracking of data changes and identification of potential security breaches. |
| Data Validation | Built-in rules to ensure data quality. | Configurable validation rules to check data consistency. | Reduces the risk of errors and inconsistencies that could compromise data privacy. |
Exploring FAIR Data Principles: Foundations and Implementation

Source: anywhereis.re
The FAIR data principles (Findable, Accessible, Interoperable, and Reusable) provide a framework for enhancing the value and utility of data. They aim to make data assets more discoverable, accessible, understandable, and ultimately, more valuable for reuse. Applying these principles, particularly in sensitive domains like healthcare, requires careful consideration of both the benefits and the challenges.
The Four Core FAIR Data Principles
The FAIR principles are a set of guidelines designed to improve the management and stewardship of data. Each principle contributes to making data more useful for both humans and machines.
- Findable: This principle ensures that data and metadata are easily discoverable. This involves assigning globally unique and persistent identifiers (like DOIs), registering data in searchable repositories, and providing rich metadata that describes the data.
- Accessible: This principle focuses on making data retrievable by both humans and machines. Data should be accessible via standardized protocols, with clear licensing and access conditions. Even if data access is restricted, the metadata should be accessible.
- Interoperable: This principle promotes the ability of data to be combined with other data. It involves using standardized data formats, vocabularies, and ontologies to ensure that data from different sources can be integrated and analyzed together.
- Reusable: This principle ensures that data can be used for different purposes. It emphasizes the need for clear licensing, detailed provenance information, and well-described metadata so that others can understand how the data was created, and how it can be used.
Applying FAIR Principles in Health Data Management: Examples
Implementing FAIR principles in health data management offers significant advantages for research, clinical care, and public health. Here are some examples:
- Findable: A hospital uses a data repository like i2b2 or a clinical data warehouse to store patient data. Each dataset receives a persistent identifier (PID), such as a Digital Object Identifier (DOI). Metadata, including descriptions of the data elements, collection methods, and data quality metrics, is made available through a metadata catalog. This allows researchers to easily discover relevant datasets for their studies.
- Accessible: Data access is controlled through a secure portal. Authorized users, such as researchers approved by an Institutional Review Board (IRB), can access de-identified patient data through a secure API. Data access is governed by clear policies and licenses, specifying permitted uses and restrictions. For example, a research team might be granted access to a dataset containing anonymized patient records for a specific study on diabetes prevalence.
- Interoperable: Hospitals adopt standardized terminologies like SNOMED CT for diagnoses and LOINC for laboratory results. Data is stored in standard formats, such as HL7 FHIR, allowing for seamless data exchange between different healthcare systems. This facilitates the integration of patient data from various sources for a comprehensive view of a patient’s health history.
- Reusable: A research team publishes a dataset of de-identified patient data, along with detailed metadata, including the study protocol, data collection instruments, and data cleaning procedures. The dataset is licensed under a Creative Commons license, allowing other researchers to reuse the data for their own studies, provided they cite the original source. The metadata also includes information about the data’s provenance, ensuring that users understand its origins and limitations.
Challenges of Implementing FAIR in a Privacy-Sensitive Environment
Implementing FAIR principles in healthcare presents unique challenges, particularly regarding patient privacy and data security. The need to balance data sharing with the protection of sensitive information requires careful planning and the use of appropriate safeguards.
- Balancing Openness and Privacy: The FAIR principles emphasize openness and accessibility, which can conflict with the need to protect patient privacy. Making data findable and accessible requires revealing information about the data, potentially including sensitive details.
- Data Anonymization and De-identification: Effectively anonymizing or de-identifying data can be complex and may not always be sufficient to prevent re-identification, especially with the availability of sophisticated data analysis techniques.
- Regulatory Compliance: Healthcare data is subject to strict regulations, such as HIPAA in the United States and GDPR in Europe. Implementing FAIR principles must comply with these regulations, which can add complexity and cost.
- Data Governance and Access Control: Establishing robust data governance frameworks and access control mechanisms is crucial to ensure that only authorized users can access data. This requires the development of clear policies, procedures, and technical controls.
- Metadata Management: While metadata is essential for FAIR, it can inadvertently reveal sensitive information if not carefully managed. Creating comprehensive metadata without compromising privacy is a significant challenge.
Methods for Ensuring Data Privacy While Adhering to FAIR Principles
Several methods can be employed to balance FAIR principles with data privacy requirements. These methods include technical, organizational, and legal approaches.
- Data Anonymization and De-identification: Techniques such as removing direct identifiers (names, addresses), generalizing values (e.g., age ranges), and using techniques like k-anonymity or differential privacy to protect against re-identification.
- Data Encryption: Encrypting data at rest and in transit to protect it from unauthorized access. This ensures that even if data is accessed, it cannot be read without the proper decryption keys.
- Access Controls and Authorization: Implementing robust access controls to restrict data access to authorized users only. This includes role-based access control, multi-factor authentication, and regular audits of access logs.
- Data Usage Agreements and Licensing: Establishing clear data usage agreements that specify the permitted uses of the data and any restrictions on its use. Licensing the data under a Creative Commons license can also help to clarify the terms of use.
- Federated Data Networks: Using federated data networks, where data remains at the source and is accessed remotely for analysis. This reduces the risk of data breaches and allows data owners to maintain control over their data.
- Privacy-Enhancing Technologies (PETs): Employing PETs, such as homomorphic encryption and secure multi-party computation, to perform computations on encrypted data without decrypting it.
- Data Governance Frameworks: Implementing comprehensive data governance frameworks that define roles, responsibilities, and processes for data management, including data privacy and security.
How Metadata Standards Contribute to FAIRness and Data Privacy
Metadata standards play a crucial role in enabling both FAIRness and data privacy. They provide a structured way to describe data, facilitating its discoverability, accessibility, interoperability, and reusability, while also enabling the implementation of privacy-preserving measures.
- Improved Findability: Standardized metadata schemas, such as Dublin Core or the Metadata Encoding and Transmission Standard (METS), enable the creation of rich metadata that can be used to search and discover data. This includes information about the data’s content, origin, and access conditions.
- Enhanced Accessibility: Metadata can specify access conditions, such as who is authorized to access the data and under what terms. This information can be used to enforce access controls and ensure that data is only accessed by authorized users.
- Increased Interoperability: Standardized metadata schemas facilitate the integration of data from different sources. Using common vocabularies and ontologies ensures that data elements are consistently defined and understood.
- Promoted Reusability: Metadata provides essential information about the data’s provenance, quality, and limitations, making it easier for users to understand how the data can be used and what its limitations are.
- Support for Privacy: Metadata can be used to document privacy-related information, such as data de-identification methods, data usage restrictions, and compliance with relevant regulations. This ensures that users are aware of the privacy implications of using the data. For example, a metadata field could indicate that a dataset has been de-identified using HIPAA Safe Harbor methods.
Comparative Analysis: DHIS2 vs. FAIR Data Approaches for Privacy
This section delves into a comparative analysis of DHIS2 and FAIR data principles, specifically focusing on their approaches to privacy. It will examine the privacy mechanisms, data security, and patient confidentiality aspects of each approach. The goal is to highlight the advantages, disadvantages, and potential synergies between DHIS2 and FAIR data principles in the context of healthcare data management.
Privacy Mechanisms: DHIS2 vs. FAIR Data Principles
DHIS2 and FAIR data principles employ distinct mechanisms for privacy protection. Understanding these differences is crucial for evaluating their effectiveness in safeguarding sensitive patient information.DHIS2 primarily relies on:
- Role-Based Access Control (RBAC): This mechanism restricts access to data based on user roles and permissions. For example, a data entry clerk might only have access to enter data, while a clinician could view and potentially modify it, and a data analyst might have access to aggregated data.
- Data Encryption: DHIS2 supports encryption at rest and in transit, protecting data from unauthorized access, even if the database is compromised.
- Audit Trails: The system logs all user actions, allowing for tracking and monitoring of data access and modifications. This facilitates accountability and helps identify potential privacy breaches.
- Data Anonymization/Pseudonymization: DHIS2 offers functionalities to anonymize or pseudonymize data, such as removing or replacing personally identifiable information (PII) with codes or aggregations, before sharing or analyzing it.
FAIR data principles, while not a privacy framework themselves, promote privacy through:
- Data Minimization: FAIR encourages the collection and use of only the minimum necessary data, reducing the risk of exposing sensitive information.
- Data De-identification: FAIR principles support the use of de-identification techniques, like anonymization and pseudonymization, to remove or obscure PII. This is critical for making data Findable, Accessible, and Reusable without compromising privacy.
- Controlled Access: FAIR emphasizes controlled access to data, often through data access agreements, data use agreements, and secure data repositories. This ensures that data is only accessed by authorized individuals for legitimate purposes.
- Metadata Standards: FAIR promotes the use of rich metadata, which can include information about data privacy and security measures, making it easier to assess the privacy risks associated with a dataset. This enhances data transparency and accountability.
Advantages and Disadvantages of Each Approach
Each approach presents distinct advantages and disadvantages concerning data security and patient confidentiality.DHIS2’s advantages include:
- Mature System: DHIS2 is a well-established system with a large user base and readily available support.
- Granular Access Control: RBAC allows for fine-grained control over data access, tailoring permissions to specific user roles.
- Auditing Capabilities: Comprehensive audit trails facilitate monitoring and accountability, enhancing data security.
- Localized Control: DHIS2 can be deployed locally, providing greater control over data storage and access, especially important in settings with limited internet connectivity or concerns about data sovereignty.
DHIS2’s disadvantages include:
- Complexity: Configuring and managing RBAC and encryption can be complex, requiring specialized technical expertise.
- Implementation Costs: Implementing and maintaining a secure DHIS2 instance can be expensive, particularly in resource-constrained settings.
- Dependence on User Compliance: The effectiveness of RBAC and other security measures depends on user adherence to security protocols.
FAIR data principles offer these advantages:
- Data Reusability: FAIR promotes data reusability, which can lead to new discoveries and insights while reducing the need for repeated data collection, potentially minimizing privacy risks.
- Data Transparency: The emphasis on metadata enhances data transparency, making it easier to understand the privacy implications of a dataset.
- Scalability: FAIR principles can be applied across a wide range of data types and platforms, facilitating data sharing and collaboration.
- Focus on Ethical Data Practices: FAIR encourages ethical data practices, which are essential for building trust and ensuring the responsible use of data.
FAIR data principles have these disadvantages:
- Implementation Challenges: Implementing FAIR principles requires significant effort and resources, particularly in terms of data standardization, metadata creation, and data governance.
- Lack of Enforcement Mechanisms: FAIR principles are guidelines, not legal mandates. Enforcement relies on data providers’ commitment and community standards.
- Data De-identification Challenges: Effective data de-identification can be complex and may not always be feasible, particularly for small datasets or data with unique identifiers.
Potential Synergies Between DHIS2 and FAIR Data Principles
DHIS2 and FAIR data principles are not mutually exclusive; they can complement each other to enhance data management practices.Potential synergies include:
- Metadata Integration: DHIS2 can be extended to incorporate FAIR-compliant metadata, such as metadata about data provenance, access conditions, and privacy measures. This would enhance data discoverability and transparency.
- Data De-identification within DHIS2: DHIS2’s data anonymization and pseudonymization features can be used to prepare data for FAIR sharing, allowing data to be made Findable, Accessible, Interoperable, and Reusable while protecting patient privacy.
- Controlled Access with DHIS2: DHIS2’s RBAC can be integrated with FAIR data access agreements to control access to sensitive data, ensuring that only authorized users can access specific datasets.
- Data Governance Alignment: Both DHIS2 and FAIR data initiatives can benefit from a robust data governance framework that defines data ownership, access policies, and data quality standards.
Comparative Table: DHIS2 vs. FAIR Approaches
This table compares DHIS2 and FAIR data approaches across several dimensions, including security, compliance, and usability.
| Feature | DHIS2 | FAIR Data Principles | Considerations |
|---|---|---|---|
| Security | RBAC, Encryption, Audit Trails, Data Anonymization/Pseudonymization | Data Minimization, Data De-identification, Controlled Access, Metadata Standards | DHIS2 focuses on technical security controls, while FAIR emphasizes data management practices to protect privacy. Both approaches are essential for a comprehensive security strategy. |
| Compliance | Supports compliance with data privacy regulations (e.g., GDPR) through access control, audit trails, and data minimization. | Facilitates compliance by promoting data transparency, ethical data practices, and data reusability, but requires specific implementation strategies to ensure compliance with privacy regulations. | Both approaches contribute to regulatory compliance, but require additional measures, such as data use agreements and privacy impact assessments, to ensure full compliance. |
| Usability | User-friendly interface for data entry, reporting, and analysis, particularly for health program managers. Requires specialized skills for security configuration. | Promotes data reusability and discoverability through standardized metadata and data formats. Implementation requires data expertise and data governance. | DHIS2 focuses on user-friendliness for operational data management, while FAIR emphasizes usability for data sharing and reuse. Both can be combined to achieve optimal results. |
| Data Governance | Typically governed by the organization or health program implementing DHIS2, with centralized control over data access and management. | Data governance often involves a broader community, with data stewards responsible for data quality, metadata creation, and data access policies. Data governance frameworks can be tailored to specific research or data-sharing needs. | DHIS2 offers a more centralized approach to data governance, while FAIR promotes a more collaborative and distributed model. Both models require clear policies and procedures for data management. |
Differences in Data Governance Models
Data governance models differ significantly between DHIS2 and FAIR data initiatives. Understanding these differences is crucial for establishing effective data management practices.DHIS2 typically operates under a centralized data governance model:
- Data Ownership: Data ownership usually resides with the implementing organization or health program.
- Access Control: Access control is managed through RBAC, with clearly defined roles and permissions.
- Data Quality: Data quality is the responsibility of the data entry staff and data managers.
- Standardization: Data standardization is usually defined by the organization or health program, with a focus on meeting specific reporting requirements.
FAIR data initiatives typically adopt a more collaborative and distributed data governance model:
- Data Ownership: Data ownership may reside with individual researchers, institutions, or data repositories.
- Access Control: Access control is managed through data use agreements, data access policies, and secure data repositories.
- Data Quality: Data quality is the responsibility of the data providers and data stewards.
- Standardization: Data standardization is driven by community standards and the adoption of widely accepted metadata schemas.
Privacy-Enhancing Technologies (PETs) and Their Integration
Data privacy is paramount in healthcare, and Privacy-Enhancing Technologies (PETs) offer crucial tools to protect sensitive patient information while enabling valuable data analysis and sharing. This section explores various PETs, their application in health data management, and how they can be integrated with DHIS2 and FAIR data principles.
Role of PETs in Enhancing Data Privacy
PETs are technologies designed to minimize privacy risks associated with data processing and sharing. They achieve this by transforming data in ways that allow for analysis and utility while limiting the exposure of sensitive information. They provide a range of techniques, each with different strengths and weaknesses, suitable for various data types and privacy requirements.
Examples of PETs Integration with DHIS2 or FAIR Data Initiatives
PETs can be integrated into both DHIS2 and FAIR data initiatives to enhance privacy. Here are a few examples:
- Differential Privacy in DHIS2: Implementing differential privacy within DHIS2 allows for the release of aggregated statistics (e.g., disease prevalence rates) without revealing individual patient data. This is achieved by adding carefully calibrated noise to the data, ensuring that the presence or absence of any single individual in the dataset does not significantly alter the results. For example, a DHIS2 instance could use differential privacy to report the number of malaria cases in a specific region, adding noise to the count to protect the privacy of patients.
- Homomorphic Encryption for FAIR Data: Homomorphic encryption enables computations on encrypted data without decryption. This is particularly useful for FAIR data initiatives where data needs to be shared across multiple organizations while maintaining privacy. Data can be encrypted before sharing, and computations can be performed on the encrypted data by authorized parties. The results are then decrypted to reveal the output. For example, researchers could use homomorphic encryption to perform a collaborative analysis of patient data from multiple hospitals, without any hospital having to share unencrypted patient records.
- Secure Multi-Party Computation (SMPC) for Collaborative Analysis: SMPC allows multiple parties to jointly compute a function on their private inputs without revealing the inputs themselves. This is valuable in FAIR data contexts where different organizations hold parts of a dataset. They can jointly compute statistics or build machine learning models without sharing raw data. For instance, several health insurance companies could use SMPC to build a model to predict the cost of healthcare services, without sharing their individual patient records.
Potential Benefits and Challenges of Using PETs in Health Data Management
Implementing PETs in health data management offers significant benefits but also presents challenges.
- Benefits:
- Enhanced Data Privacy: PETs significantly reduce the risk of data breaches and unauthorized access to sensitive patient information.
- Increased Data Sharing: By protecting privacy, PETs encourage greater data sharing among healthcare providers, researchers, and public health agencies, which can improve healthcare delivery and research outcomes.
- Regulatory Compliance: PETs help organizations comply with data privacy regulations such as HIPAA, GDPR, and others.
- Improved Trust: The use of PETs can build trust among patients and the public, leading to greater participation in health initiatives.
- Challenges:
- Complexity: Implementing PETs can be complex, requiring specialized expertise and infrastructure.
- Computational Overhead: Some PETs, such as homomorphic encryption, can introduce significant computational overhead, slowing down data processing and analysis.
- Utility Trade-offs: Some PETs may reduce the utility of the data, especially when using techniques like differential privacy, which adds noise to the data. Finding the right balance between privacy and utility is critical.
- Interoperability: Ensuring that different PETs work together and integrate seamlessly with existing health IT systems can be challenging.
List of PETs and Their Suitability for Different Types of Health Data
The suitability of a PET depends on the type of health data and the desired level of privacy.
| Privacy-Enhancing Technology (PET) | Description | Suitability for Health Data Types | Examples of Use Cases |
|---|---|---|---|
| Differential Privacy | Adds noise to data to protect individual privacy. | Aggregated statistics, demographic data, public health reports. | Reporting disease prevalence rates, tracking vaccination coverage. |
| Homomorphic Encryption | Allows computations on encrypted data. | Research data, clinical trial data, shared patient records. | Collaborative analysis of patient data, secure data sharing across organizations. |
| Secure Multi-Party Computation (SMPC) | Enables joint computation without revealing individual inputs. | Data from multiple sources, collaborative research, insurance data. | Jointly building predictive models, calculating risk scores across different healthcare providers. |
| Federated Learning | Trains machine learning models across decentralized data sources without sharing raw data. | Clinical data, imaging data, patient outcomes data. | Developing predictive models for disease diagnosis or treatment outcomes. |
| Data Masking/Pseudonymization | Replaces or removes identifying information. | Clinical records, research datasets, billing information. | De-identifying patient records for research, creating masked datasets for analysis. |
Conceptual Diagram: Integration of PETs with DHIS2 and FAIR Data Approaches
Imagine a diagram that illustrates the flow of data and security layers when integrating PETs with DHIS2 and FAIR data principles.
Diagram Description:The diagram is structured to show a flow of data, starting with data sources (e.g., electronic health records, lab systems) and progressing through various stages of processing and analysis, with security measures layered throughout.
1. Data Sources
On the left side, various data sources such as EHRs and lab systems are shown. Each source is depicted as a distinct box.
2. Data Ingestion and Preprocessing Layer
The data from these sources flows into a preprocessing layer. This layer includes functions such as data cleaning, transformation, and potentially pseudonymization or data masking to remove direct identifiers. This layer is shown as a rectangular box that receives input from the data sources.
3. DHIS2 Integration (Centralized Data Storage)
Data from the preprocessing layer is fed into DHIS2. This integration is shown as an arrow leading to a DHIS2 server, depicted as a central box. Within DHIS2, the data can be further processed for reporting and analysis. For privacy, differential privacy can be applied to aggregate data generated by DHIS2, before it is shared.
4. FAIR Data Principles and Data Sharing (Decentralized Data Access)
Another path from the preprocessing layer leads to a FAIR data platform. This platform uses homomorphic encryption and SMPC to allow secure data sharing and analysis. Data is encrypted before sharing and computation is performed on encrypted data. The FAIR data platform is shown as a box where multiple entities can interact with the data.
5. PETs Integration
The diagram shows where different PETs are integrated.
- Differential Privacy: Applied to aggregated data generated by DHIS2. This adds noise to protect individual privacy when generating reports.
- Homomorphic Encryption: Used in the FAIR data platform to allow computation on encrypted data.
- SMPC: Used in the FAIR data platform to allow collaborative computation on data from multiple sources without revealing the raw data.
6. Security Layers
The entire diagram is surrounded by security layers to protect the data. This includes:
- Encryption: Data is encrypted at rest and in transit.
- Access Control: Strict access controls are implemented to limit who can access the data.
- Auditing: All data access and processing activities are audited to ensure accountability.
7. Data Output and Analysis
The final output of the diagram includes:
- Reports and Dashboards: Generated by DHIS2 using differentially private data.
- Research Findings: Generated by the FAIR data platform through secure computation.
Case Studies: Real-World Examples and Implementations
Examining real-world applications is crucial to understanding the practical implications of both DHIS2 and FAIR data principles for data privacy in healthcare. These case studies highlight successful implementations, lessons learned, and the effectiveness of various approaches in safeguarding sensitive patient information. They provide tangible examples of how these technologies and principles are applied to address data privacy challenges.
These case studies showcase the diverse ways organizations have approached data privacy, illustrating both the strengths and limitations of each approach. By analyzing these examples, we can gain valuable insights into best practices and identify areas for improvement in data privacy strategies.
DHIS2 Implementations Addressing Data Privacy
Several DHIS2 implementations have prioritized data privacy by incorporating robust security measures and adhering to relevant regulations. These examples demonstrate how DHIS2 can be configured to protect sensitive health data while still enabling effective data collection and analysis. Here are some notable examples:
- Kenya’s Integrated Disease Surveillance and Response (IDSR) System: This system, built on DHIS2, collects and manages data related to disease outbreaks and public health interventions. To address privacy concerns, the system implements role-based access control, ensuring that only authorized personnel can access specific data. Data is de-identified where possible, and audit trails are maintained to track data access and modifications. Furthermore, the system adheres to Kenyan data protection regulations.
- Uganda’s Health Management Information System (HMIS): The Ugandan HMIS, also utilizing DHIS2, collects a wide range of health data, including patient demographics and clinical information. Privacy measures include data encryption both in transit and at rest, secure user authentication, and regular security audits. Data sharing agreements are in place to govern data exchange with external partners, and data anonymization techniques are employed for research purposes.
- Ethiopia’s Electronic Health Records (EHR) System: Ethiopia’s EHR system, integrated with DHIS2, focuses on digitizing patient records. Data privacy is a core concern, with the system utilizing encryption, access controls based on user roles, and data minimization strategies. Patients are given control over their data through patient portals, and consent management is integrated into the system. The system complies with Ethiopian data protection guidelines.
These DHIS2 implementations emphasize the importance of a layered approach to data privacy, combining technical safeguards with robust organizational policies and procedures.
FAIR Data Principles in Healthcare: Real-World Projects
The FAIR data principles – Findability, Accessibility, Interoperability, and Reusability – are increasingly being adopted in healthcare to improve data sharing and promote research while addressing privacy concerns. Several projects demonstrate the practical application of these principles. Here are some examples:
- The European Genome-phenome Archive (EGA): EGA is a service for archiving and sharing personally identifiable genetic and phenotypic data. It is designed to ensure that data can be shared securely and ethically. Data access is controlled based on informed consent and ethical review. The EGA utilizes a controlled access model, where researchers must apply for access to specific datasets and agree to terms of use.
Data is de-identified and encrypted, and access is monitored and audited.
- The All of Us Research Program: This large-scale research program in the United States aims to collect and share health data from a diverse population. It adheres to FAIR principles by making data findable through a data catalog, accessible through controlled access, interoperable through standardized formats, and reusable for various research purposes. The program emphasizes patient privacy by de-identifying data, obtaining informed consent, and implementing data security measures.
- The Observational Health Data Sciences and Informatics (OHDSI) Initiative: OHDSI is a collaborative initiative that uses FAIR principles to create and analyze observational health data. It promotes data interoperability by using the OMOP Common Data Model, enabling researchers to analyze data from different sources in a standardized way. Privacy is addressed through data de-identification, secure data transfer protocols, and adherence to relevant regulations.
These projects illustrate how FAIR data principles can facilitate responsible data sharing and reuse in healthcare while protecting patient privacy. The emphasis is on balancing the benefits of data sharing with the need to safeguard sensitive information.
Lessons Learned: Data Privacy Best Practices
Analyzing these case studies reveals several key lessons regarding data privacy best practices:
- Comprehensive Privacy Policies: Implementing clear and comprehensive privacy policies that Artikel data handling procedures, data access controls, and data breach response plans is crucial. These policies should be regularly reviewed and updated to reflect evolving privacy regulations and best practices.
- Role-Based Access Control: Employing role-based access control (RBAC) ensures that only authorized personnel can access specific data based on their roles and responsibilities. This minimizes the risk of unauthorized data access and data breaches.
- Data Encryption: Encrypting data both in transit and at rest is essential for protecting sensitive information from unauthorized access. This includes encrypting data stored in databases, transmitted over networks, and stored on backup media.
- Data De-identification and Anonymization: De-identifying or anonymizing data, whenever possible, reduces the risk of re-identification and protects patient privacy. This includes removing or masking direct identifiers and using techniques such as k-anonymity and differential privacy.
- Regular Security Audits and Monitoring: Conducting regular security audits and monitoring data access logs helps identify and address potential security vulnerabilities and data breaches. This includes monitoring user activity, reviewing system logs, and conducting penetration testing.
- Patient Consent and Data Control: Providing patients with control over their data, including the ability to access, modify, and revoke consent, is essential for building trust and ensuring ethical data practices. This includes implementing patient portals and consent management systems.
- Adherence to Data Protection Regulations: Complying with relevant data protection regulations, such as GDPR, HIPAA, and national data protection laws, is crucial for ensuring legal compliance and protecting patient privacy. This includes appointing a Data Protection Officer (DPO) and implementing data processing agreements.
- Data Sharing Agreements: Establishing data sharing agreements with external partners ensures that data is shared securely and ethically. These agreements should Artikel data access controls, data usage restrictions, and data breach response plans.
- Training and Awareness: Providing regular training and awareness programs to staff on data privacy best practices helps ensure that everyone understands their responsibilities in protecting patient data.
These lessons highlight the importance of a holistic approach to data privacy, combining technical safeguards, robust organizational policies, and a culture of data protection.
Comparative Effectiveness: DHIS2 and FAIR Data Approaches
Here’s a comparison of how both approaches address data privacy:
- DHIS2:
- Strengths: Provides granular control over data access through RBAC, supports data encryption and audit trails, and can be customized to comply with local regulations. It is well-suited for managing health data within a specific organizational context.
- Weaknesses: May face challenges in data interoperability with other systems and can require significant customization to implement advanced privacy-enhancing technologies. Sharing data outside of the immediate system requires careful consideration of data sharing agreements.
- FAIR Data Principles:
- Strengths: Promotes data findability, accessibility, interoperability, and reusability, enabling wider data sharing and research opportunities. Encourages the use of standardized data formats and controlled access mechanisms.
- Weaknesses: Implementation can be complex, requiring the adoption of data standards and governance frameworks. May require investment in data infrastructure and expertise. Privacy must be carefully managed through access controls and de-identification techniques.
- Combined Approach:
- Effectiveness: Integrating FAIR principles with a DHIS2 implementation can enhance data sharing capabilities while maintaining strong privacy controls. DHIS2 can serve as a data repository that adheres to FAIR principles, allowing data to be findable, accessible (through controlled access), interoperable (using standardized data formats), and reusable (with appropriate data usage agreements).
- Example: A DHIS2 instance could be configured to use a standardized data model, like the OMOP Common Data Model, to facilitate interoperability. Data could be de-identified and made accessible through a secure portal, adhering to FAIR principles. Access would be controlled through DHIS2’s RBAC system, and data sharing agreements would govern the use of the data.
The optimal approach often involves a combination of both DHIS2 and FAIR data principles, leveraging the strengths of each to create a robust and privacy-conscious data management system.
Future Directions: Bridging the Gap and Fostering Innovation
Source: website-files.com
The landscape of healthcare data management is constantly evolving, with new technologies and approaches emerging to address the critical balance between data accessibility and patient privacy. This section explores potential future developments in DHIS2 and FAIR data principles, highlighting emerging trends, providing recommendations, and emphasizing the importance of collaboration in driving innovation.
Potential Future Developments in DHIS2 and FAIR Data Approaches
DHIS2 and FAIR data approaches are poised for significant advancements that will enhance data privacy. These advancements are driven by the need to meet the growing demands for data-driven healthcare while ensuring patient confidentiality.* DHIS2 Enhancements: DHIS2 could integrate more robust privacy features, such as:
Enhanced data anonymization and pseudonymization tools.
Improved access control mechanisms based on roles and permissions.
Integration with privacy-enhancing technologies (PETs) like secure multi-party computation (SMPC) to enable analysis without revealing individual patient data.
FAIR Data Approach Refinements
The FAIR principles can be strengthened to better address privacy concerns:
Develop more standardized metadata schemas that include privacy-related information.
Create tools and guidelines for data custodians to implement privacy-preserving data management practices.
Establish clear mechanisms for data access requests that balance the needs of researchers with patient privacy rights.
Emerging Trends and Technologies for Data Security and Patient Confidentiality
Several emerging trends and technologies hold promise for improving data security and patient confidentiality in healthcare.* Blockchain Technology: Blockchain can be used to create secure and transparent data sharing platforms.
Example
Implementing blockchain for managing patient consent records, ensuring that patients have control over their data and can track who accesses it.
Federated Learning
This allows machine learning models to be trained across decentralized datasets without directly sharing the data.
Example
Training a model to predict disease outbreaks using data from multiple hospitals without exposing individual patient records.
Homomorphic Encryption
Enables computations to be performed on encrypted data without decrypting it.
Example
Allowing researchers to analyze sensitive patient data without ever having access to the unencrypted information.
Differential Privacy
Adds noise to data to protect individual privacy while still allowing for meaningful statistical analysis.
Example
Using differential privacy to publish aggregate statistics about patient populations while preventing the identification of individuals.
Secure Multiparty Computation (SMPC)
Allows multiple parties to jointly compute a function on their inputs without revealing the inputs to each other.
Example
Multiple hospitals can collaborate to analyze data to improve patient outcomes while protecting patient privacy.
Recommendations for Healthcare Organizations
Healthcare organizations must adopt a proactive approach to balance data accessibility and privacy protection.* Implement Robust Data Governance Policies: Develop clear policies and procedures for data collection, storage, access, and sharing. These policies should align with relevant regulations such as HIPAA and GDPR.
Prioritize Data Security
Invest in robust cybersecurity measures to protect data from unauthorized access, breaches, and cyberattacks. This includes implementing firewalls, intrusion detection systems, and regular security audits.
Embrace Privacy-Enhancing Technologies (PETs)
Explore and implement PETs like those mentioned above to protect patient data while enabling data analysis and research.
Invest in Training and Education
Provide training to staff on data privacy best practices, data security protocols, and the ethical use of patient data.
Foster a Culture of Privacy
Create a culture where data privacy is a top priority, with all staff members understanding their roles and responsibilities in protecting patient information.
Conduct Regular Privacy Audits
Perform regular audits to assess the effectiveness of privacy controls and identify areas for improvement.
Best Practices for the Future of Health Data Management
Data Minimization
Collect and store only the data necessary for the intended purpose.
Data Anonymization/Pseudonymization
Employ techniques to remove or replace identifying information.
Access Control
Implement strict access controls based on the principle of least privilege.
Data Encryption
Encrypt data at rest and in transit.
Regular Auditing
Conduct regular audits to monitor data access and usage.
Transparency and Consent
Obtain informed consent for data collection and usage, and be transparent about data practices.
Compliance
Adhere to all relevant data privacy regulations.
Data Stewardship
Designate data stewards responsible for data quality, security, and privacy.
Collaborations and Partnerships for Innovation
Collaborations and partnerships are essential for driving innovation in health data management.* Academic Institutions: Partner with universities and research institutions to develop new privacy-enhancing technologies and conduct research on data security.
Technology Companies
Collaborate with technology companies to integrate new tools and platforms for data management and analysis.
Healthcare Providers
Work with healthcare providers to implement new data management solutions and ensure they meet the needs of clinicians and patients.
Government Agencies
Collaborate with government agencies to develop and implement data privacy regulations and guidelines.
International Organizations
Engage with international organizations to promote the adoption of best practices for health data management and foster global collaboration.
Final Thoughts
In conclusion, the journey through DHIS2 and FAIR data approaches highlights the complex balance between data accessibility and privacy. While both offer unique strengths, their combined potential, especially with the integration of Privacy-Enhancing Technologies, promises a future where health data is both readily available for research and securely protected. By embracing best practices and fostering collaboration, we can move towards a more transparent and trustworthy health data ecosystem, ensuring patient confidentiality while driving innovation in healthcare.
Question Bank
What is DHIS2?
DHIS2 (District Health Information Software 2) is an open-source platform used for collecting, managing, and analyzing health data, particularly in resource-constrained settings. It supports a wide range of health programs and indicators.
What are FAIR data principles?
FAIR data principles (Findable, Accessible, Interoperable, and Reusable) are a set of guidelines designed to make data more discoverable, accessible, usable, and reusable for both humans and machines.
How do DHIS2 and FAIR data principles relate to data privacy?
Both DHIS2 and FAIR principles aim to manage data effectively, but they approach privacy differently. DHIS2 offers built-in security features, while FAIR principles emphasize data sharing, which can pose privacy challenges. Balancing these approaches requires careful implementation and the use of privacy-enhancing technologies.
What are Privacy-Enhancing Technologies (PETs)?
PETs are technologies that help protect individual privacy while enabling data analysis and sharing. Examples include differential privacy, homomorphic encryption, and secure multi-party computation.
Can DHIS2 be made FAIR?
Yes, DHIS2 can be adapted to align with FAIR principles. This involves implementing metadata standards, using unique identifiers, and providing secure and controlled access to data, often through the use of additional tools and technologies.